Announcing Heeler Endpoints: Mapping and Securing AI-Generated Attack Surfaces

Today, we are thrilled to announce a major expansion of the Heeler platform: Endpoints.
As AI-driven development and complex microservices accelerate code production, the visibility gap for endpoints has become a severe security issue.
This isn't just another inventory tool. It is a framework-aware analysis engine designed specifically to handle the sheer volume of modern code: transforming how security and engineering teams visualize, prioritize, and secure their entire application attack surface without ever touching runtime agents.
Why This Matters for Modern Security Teams
- Live API Inventory: Move from stale manual docs to a real-time catalog of 100+ frameworks.
- Identify Risk: Instantly identify unauthenticated, internet-facing APIs.
- High-Fidelity SAST Triage: Eliminate alert fatigue. We use reachability and taint analysis to prove which vulnerabilities are truly exploitable, saving your team hours in manual triage.
- Automated Threat Modeling: Accelerate code-to-cloud derived architecture context via Service Decomposition.
- AI Attack Surface Control: Shine a light on AI-generated code by discovering MCP tools automatically.
- Systematic Posture Analysis: Move beyond spot checks to automated analysis of CORS, CSRF, and Auth enforcement.
The Challenge: AI-Generated APIs and the Scrutiny Gap
One of the most pressing challenges our customers face is the explosion of endpoints brought on by AI-assisted coding. While LLMs help developers ship at a 10x pace, they frequently introduce new endpoints, MCP tools, and boilerplate routes that bypass traditional architectural reviews.
This AI-generated code often introduces significant new functionality that faces far less human scrutiny than manually written code. The result? An explosion of Shadow APIs and unvetted AI integrations that security teams didn't even know existed. Heeler addresses this head-on by performing deep source code analysis across 13 programming languages and over 100 web frameworks, automatically synthesizing a live inventory of every interface in your codebase.
Heeler performs deep source code analysis to identify and classify endpoints across a wide range of frameworks and protocols:
- REST APIs:Standard HTTP endpoints detected through framework-specific decorators, annotations, route registration calls, and class-based handler patterns
- MCP Tools, Resources, and Prompts: Model Context Protocol interfaces exposed by AI agent frameworks, with transport type and capability analysis
- Spring Boot Actuator Endpoints: Management and monitoring endpoints synthesized from dependency manifests and configuration files, with detailed exposure and sensitivity analysis across 26 actuator groups and 50+ routes
- GraphQL: Query and mutation resolvers
- gRPC: Remote procedure call service definitions
- SOAP: XML-based web services (ASMX, WCF)
- WebSocket and Webhook:Real-time and event-driven interfaces
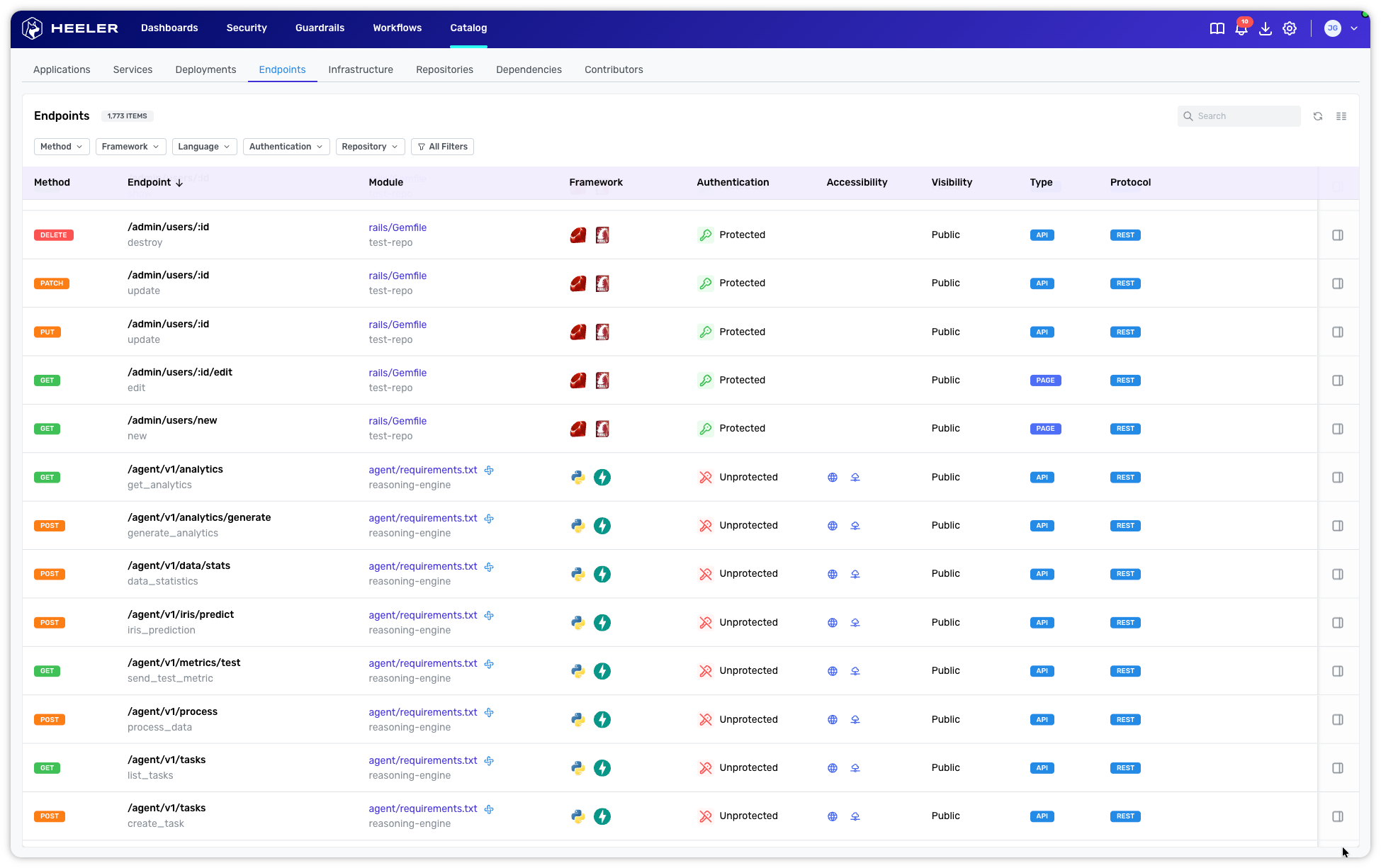
Granular Visibility at Scale
Heeler doesn't just list paths; it provides a comprehensive identity for every interface. Each entry in the Endpoints catalog provides deep context, including:
- Method: Detects standard HTTP methods (GET, POST, etc.) alongside interface types like MCP_TOOL, MCP_PROMPT, and MCP_RESOURCE.
- Endpoint Details: Maps the exact route path and links it directly to the underlying handler function name.
- Module & Repository: Identifies the specific code module and repository, with direct links to the source code for immediate investigation.
- Framework Context: Surfaces the detected framework (e.g., Spring, FastAPI, Express) with associated language icons.
- Authentication Posture: Provides visual indicators of whether the endpoint is protected or unprotected.
- Accessibility & Visibility: Determines if an endpoint is internet-accessible/internet-facing and defines its scope (Public, Internal, Private, or Restricted).
- Classification & Protocol: Badges each entry by type (API, MCP, or Page) and protocol (REST, GraphQL, gRPC, MCP, or SOAP).
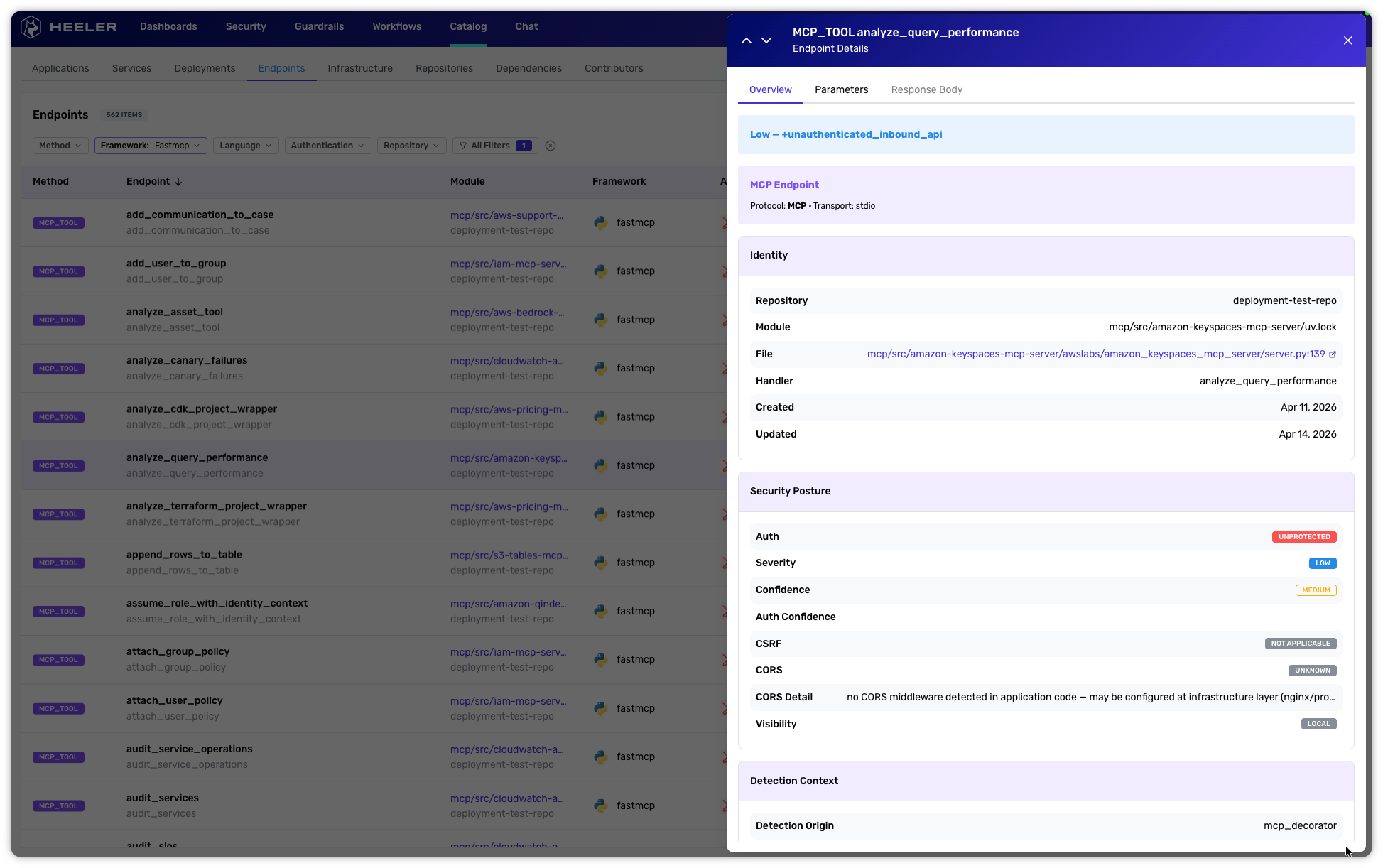
Benefit 1: Instant Risk Identification
Visibility is only valuable if it leads to action. Heeler provides the ability to immediately identify at-risk APIs based on a comprehensive evaluation of security posture. By correlating three critical data points, Heeler surfaces high-risk exposures in real-time:
- Authentication Status: An eight-layer analysis pipeline traces middleware, decorators (like @PreAuthorize), and dependency injection chains to determine if an endpoint is truly protected.
- Visibility Scope: Heeler classifies endpoints as public, internal, private, or restricted based on implementation context.
- Internet Reachability: By combining configuration files and deployment topology, Heeler determines whether an endpoint is internet-accessible or internet-facing.
Teams can now quickly and easily identify when an AI-generated service accidentally exposes a sensitive management port or a "public" endpoint without an auth guard,
Benefit 2: Industry-Leading SAST Auto-Triage Capabilities
The introduction of Endpoints allows Heeler to offer the industry's most powerful auto-triage of SAST (Static Application Security Testing) findings. Traditionally, SAST is plagued by noise because it lacks the context of how data actually enters or leaves an application. By providing a complete map of the attack surface, Heeler shifts the paradigm from "possible" vulnerabilities to "proven" risks.
Through Cross-File Handler Chain Graphing and Precise Source-to-Sink Tracing, Heeler confirms whether a vulnerability is actually reachable in the live execution path. Because Heeler traces the exact path from the API entry point (the source) to the vulnerable function (the sink), we transform theoretical bugs into proven, actionable risks, while automatically filtering out the noise that burns out AppSec teams.
Benefit 3: Automated Architecture Context for Threat Modeling
Beyond immediate vulnerability detection, the Endpoints catalog serves as the foundation for modern security reviews. By capturing the complete interface of every service, Heeler enriches your runtime threat modeling and security review context.
This data is included in Heeler’s Service Decomposition Export, allowing security architects to export a real-time view of the running application. Instead of manually sketching data flows, teams can now leverage high-fidelity, code-derived maps of services, endpoints, and their interdependencies. This automates the discovery phase of threat modeling, ensuring that your security reviews are based on the ground truth of the code-to-cloud rather than outdated documentation.
Specialized Visibility: From Spring Boot to AI Agents
The new Endpoints view is purpose-built for the complexities of 2026:
- Spring Boot Actuators: Heeler classifies these by sensitivity (Critical to Low), flagging risks like /shutdown while accounting for compensating controls like management port isolation.
- MCP (Model Context Protocol): As AI agents become core to your stack, Heeler provides visibility into MCP server implementations, ensuring your AI integrations aren't creating unmonitored backdoors.
Get Started
With Heeler Endpoints, you finally have the visibility needed to see your code as it truly exists: exposed, authenticated, and understood, no matter who (or what) wrote it.
Ready to see your attack surface in high definition? Sign up for a free trial to see your Endpoints in Heeler.
.svg)


.jpg)

